How to Prevent CSRF Vulnerabilities. See the CSRF Prevention Cheat Sheet for prevention measures. Listen to the OWASP Top Ten CSRF Podcast. Most frameworks have built-in CSRF support such as Joomla, Spring, Struts, Ruby on Rails,.NET and others. Use OWASP CSRF Guard to add CSRF protection to your Java. See the OWASP CSRF Prevention Cheat Sheet for prevention measures. OWASP ZAP; CSRF Tester; Pinata-csrf-tool; References. Peter W: “Cross-Site Request Forgeries” Thomas Schreiber: “Session Riding” Oldest known post; Cross-site Request Forgery FAQ; A Most-Neglected Fact About Cross Site Request Forgery (CSRF) Multi-POST CSRF.
- Owasp Csrf Prevention Cheat Sheet 2020
- Owasp Csrf Prevention
- Owasp Csrf Prevention Cheat Sheet Pdf
- Owasp Csrf Prevention Cheat Sheet Download
Authentication is the process of verification that an individual, entity or website is who it claims to be. Authentication in the context of web applications is commonly performed by submitting a user name or ID and one or more items of private information that only a given user should know.
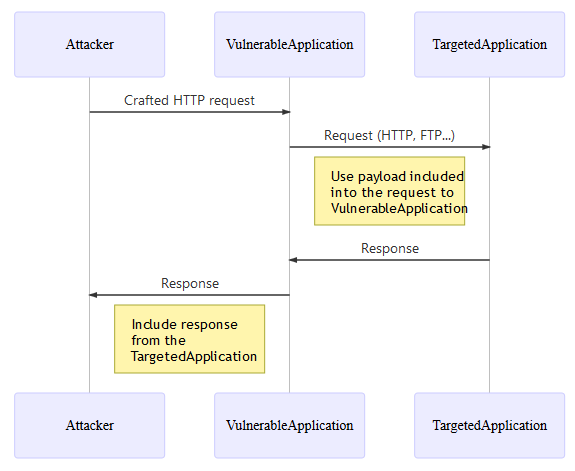
- The objective of the cheat sheet is to provide advices regarding the protection against Server Side Request Forgery (SSRF) attack. This cheat sheet will focus on the defensive point of view and will not explain how to perform this attack.
- For more ways of preventing CSRF attacks, you can refer to the OWASP CSRF Prevention Cheat Sheet. If you ever need Vulnerability Assessment and Penetration Testing done on your web application or want to make sure that vulnerabilities such as CSRF don’t end up harming your business or your customers’ online data, you can always come talk to.
Session Management is a process by which a server maintains the state of an entity interacting with it. This is required for a server to remember how to react to subsequent requests throughout a transaction. Sessions are maintained on the server by a session identifier which can be passed back and forward between the client and server when transmitting and receiving requests. Sessions should be unique per user and computationally very difficult to predict.
User IDs
Make sure your usernames/userids are case insensitive. User 'smith' and user 'Smith' should be the same user. User names should also be unique. For high security applications usernames could be assigned and secret instead of user-defined public data.
Email address as a User ID
For information on validating email addresses, please visit the input validation cheatsheet email discussion.
Authentication Solution and Sensitive Accounts
- Do NOT allow login with sensitive accounts (i.e. accounts that can be used internally within the solution such as to a back-end / middle-ware / DB) to any front end user interface
- Do NOT use the same authentication solution (e.g. IDP / AD) used internally for unsecured access (e.g. public access / DMZ)
Implement Proper Password Strength Controls
A key concern when using passwords for authentication is password strength. A 'strong' password policy makes it difficult or even improbable for one to guess the password through either manual or automated means. The following characteristics define a strong password:
Password Length
Longer passwords provide a greater combination of characters and consequently make it more difficult for an attacker to guess.
- Minimum length of the passwords should be enforced by the application.
- Passwords shorter than 10 characters are considered to be weak (NIST SP800-132).
While minimum length enforcement may cause problems with memorizing passwords among some users, applications should encourage them to set passphrases (sentences or combination of words) that can be much longer than typical passwords and yet much easier to remember.
- Maximum password length should not be set too low, as it will prevent users from creating passphrases. Typical maximum length is 128 characters.
- Passphrases shorter than 20 characters are usually considered weak if they only consist of lower case Latin characters.
Password Complexity
Applications should enforce password complexity rules to discourage easy to guess passwords. Password mechanisms should allow virtually any character the user can type to be part of their password, including the space character. Passwords should, obviously, be case sensitive in order to increase their complexity. Occasionally, we find systems where passwords aren't case sensitive, frequently due to legacy system issues like old mainframes that didn't have case sensitive passwords.
The password change mechanism should require a minimum level of complexity that makes sense for the application and its user population. Free emulators onlineeverstore. For example:
- Password must meet at least 3 out of the following 4 complexity rules
- at least 1 uppercase character (A-Z)
- at least 1 lowercase character (a-z)
- at least 1 digit (0-9)
- at least 1 special character (punctuation) — do not forget to treat space as special characters too
- at least 10 characters
- at most 128 characters
- not more than 2 identical characters in a row (e.g., 111 not allowed)
Further reading:
- Your Password Complexity Requirements are Worthless - OWASP AppSecUSA 2014 presentation for further discussion of legacy password complexity rules
Password Topologies
- Ban commonly used password topologies
- Force multiple users to use different password topologies
- Require a minimum topology change between old and new passwords
Additional Information
- Make sure that every character the user types in is actually included in the password. We've seen systems that truncate the password at a length shorter than what the user provided (e.g., truncated at 15 characters when they entered 20).
- As application's require more complex password policies, they need to be very clear about what these policies are. The required policy needs to be explicitly stated on the password change page
- If the new password doesn't comply with the complexity policy, the error message should describe EVERY complexity rule that the new password does not comply with, not just the 1st rule it doesn't comply with.
Implement Secure Password Recovery Mechanism
It is common for an application to have a mechanism that provides a means for a user to gain access to their account in the event they forget their password. Please see Forgot Password Cheat Sheet for details on this feature.
Store Passwords in a Secure Fashion
It is critical for a application to store a password using the right cryptographic technique. Please see Password Storage Cheat Sheet for details on this feature.
Transmit Passwords Only Over TLS or Other Strong Transport

See: Transport Layer Protection Cheat Sheet
The login page and all subsequent authenticated pages must be exclusively accessed over TLS or other strong transport. The initial login page, referred to as the 'login landing page', must be served over TLS or other strong transport. Failure to utilize TLS or other strong transport for the login landing page allows an attacker to modify the login form action, causing the user's credentials to be posted to an arbitrary location. Failure to utilize TLS or other strong transport for authenticated pages after login enables an attacker to view the unencrypted session ID and compromise the user's authenticated session.
Require Re-authentication for Sensitive Features
In order to mitigate CSRF and session hijacking, it's important to require the current credentials for an account before updating sensitive account information such as the user's password, user's email, or before sensitive transactions, such as shipping a purchase to a new address. Without this countermeasure, an attacker may be able to execute sensitive transactions through a CSRF or XSS attack without needing to know the user's current credentials. Additionally, an attacker may get temporary physical access to a user's browser or steal their session ID to take over the user's session.
Consider Strong Transaction Authentication
Some applications should use a second factor to check whether a user may perform sensitive operations. For more information see the Transaction Authorization Cheat Sheet.
TLS Client Authentication
TLS Client Authentication, also known as two-way TLS authentication, consists of both, browser and server, sending their respective TLS certificates during the TLS handshake process. Just as you can validate the authenticity of a server by using the certificate and asking a well known Certificate Authority (CA) if the certificate is valid, the server can authenticate the user by receiving a certificate from the client and validating against a third party CA or its own CA. To do this, the server must provide the user with a certificate generated specifically for him, assigning values to the subject so that these can be used to determine what user the certificate should validate. The user installs the certificate on a browser and now uses it for the website.
It is a good idea to do this when:
- It is acceptable (or even preferred) that the user only has access to the website from only a single computer/browser.
- The user is not easily scared by the process of installing TLS certificates on his browser or there will be someone, probably from IT support, that will do this for the user.
- The website requires an extra step of security.
- It is also a good thing to use when the website is for an intranet of a company or organization.
It is generally not a good idea to use this method for widely and publicly available websites that will have an average user. For example, it wouldn't be a good idea to implement this for a website like Facebook. While this technique can prevent the user from having to type a password (thus protecting against an average keylogger from stealing it), it is still considered a good idea to consider using both a password and TLS client authentication combined.
For more information, see: Client-authenticated TLS handshake
Authentication and Error Messages
Incorrectly implemented error messages in the case of authentication functionality can be used for the purposes of user ID and password enumeration. An application should respond (both HTTP and HTML) in a generic manner.
Authentication Responses
An application should respond with a generic error message regardless of whether the user ID or password was incorrect. It should also give no indication to the status of an existing account.
Incorrect Response Examples
- 'Login for User foo: invalid password'
- 'Login failed, invalid user ID'
- 'Login failed; account disabled'
- 'Login failed; this user is not active'
Correct Response Example
- 'Login failed; Invalid userID or password'
The correct response does not indicate if the user ID or password is the incorrect parameter and hence inferring a valid user ID.
Error Codes and URLs
The application may return a different HTTP Error code depending on the authentication attempt response. It may respond with a 200 for a positive result and a 403 for a negative result. Even though a generic error page is shown to a user, the HTTP response code may differ which can leak information about whether the account is valid or not.
Prevent Brute-Force Attacks
If an attacker is able to guess passwords without the account becoming disabled due to failed authentication attempts, the attacker has an opportunity to continue with a brute force attack until the account is compromised. Automating brute-force/password guessing attacks on web applications is a trivial challenge. Password lockout mechanisms should be employed that lock out an account if more than a preset number of unsuccessful login attempts are made. Password lockout mechanisms have a logical weakness. An attacker that undertakes a large number of authentication attempts on known account names can produce a result that locks out entire blocks of user accounts. Given that the intent of a password lockout system is to protect from brute-force attacks, a sensible strategy is to lockout accounts for a period of time (e.g., 20 minutes). This significantly slows down attackers, while allowing the accounts to reopen automatically for legitimate users.
Also, multi-factor authentication is a very powerful deterrent when trying to prevent brute force attacks since the credentials are a moving target. When multi-factor is implemented and active, account lockout may no longer be necessary.
Enable logging and monitoring of authentication functions to detect attacks / failures on a real time basis
- Ensure that all failures are logged and reviewed
- Ensure that all password failures are logged and reviewed
- Ensure that all account lockouts are logged and reviewed
While authentication through a user/password combination and using multi-factor authentication is considered generally secure, there are use cases where it isn't considered the best option or even safe. Examples of this are third party applications that desire connecting to the web application, either from a mobile device, another website, desktop or other situations. When this happens, it is NOT considered safe to allow the third party application to store the user/password combo, since then it extends the attack surface into their hands, where it isn't in your control. For this, and other use cases, there are several authentication protocols that can protect you from exposing your users' data to attackers.
OAuth
Open Authorization (OAuth) is a protocol that allows an application to authenticate against a server as a user, without requiring passwords or any third party server that acts as an identity provider. It uses a token generated by the server, and provides how the authorization flows most occur, so that a client, such as a mobile application, can tell the server what user is using the service.
The recommendation is to use and implement OAuth 1.0a or OAuth 2.0, since the very first version (OAuth1.0) has been found to be vulnerable to session fixation.
OAuth 2.0 relies on HTTPS for security and is currently used and implemented by API's from companies such as Facebook, Google, Twitter and Microsoft. OAuth1.0a is more difficult to use because it requires the use of cryptographic libraries for digital signatures. However, since OAuth1.0a does not rely on HTTPS for security it can be more suited for higher risk transactions.
OpenId
OpenId is an HTTP-based protocol that uses identity providers to validate that a user is who he says he is. It is a very simple protocol which allows a service provider initiated way for single sign-on (SSO). This allows the user to re-use a single identity given to a trusted OpenId identity provider and be the same user in multiple websites, without the need to provide any website the password, except for the OpenId identity provider.
Due to its simplicity and that it provides protection of passwords, OpenId has been well adopted. Some of the well known identity providers for OpenId are Stack Exchange, Google, Facebook and Yahoo!
For non-enterprise environments, OpenId is considered a secure and often better choice, as long as the identity provider is of trust.
SAML
Security Assertion Markup Language (SAML) is often considered to compete with OpenId. The most recommended version is 2.0, since it is very feature complete and provides a strong security. Like OpenId, SAML uses identity providers, but unlike OpenId, it is XML-based and provides more flexibility. SAML is based on browser redirects which send XML data. Furthermore, SAML isn't only initiated by a service provider; it can also be initiated from the identity provider. This allows the user to navigate through different portals while still being authenticated without having to do anything, making the process transparent.
While OpenId has taken most of the consumer market, SAML is often the choice for enterprise applications. The reason for this is often that there are few OpenId identity providers which are considered of enterprise class (meaning that the way they validate the user identity doesn't have high standards required for enterprise identity). It is more common to see SAML being used inside of intranet websites, sometimes even using a server from the intranet as the identity provider.
In the past few years, applications like SAP ERP and SharePoint (SharePoint by using Active Directory Federation Services 2.0) have decided to use SAML 2.0 authentication as an often preferred method for single sign-on implementations whenever enterprise federation is required for web services and web applications.
See also: SAML Security Cheat Sheet
FIDO
The Fast Identity Online (FIDO) Alliance has created two protocols to facilitate online authentication : the Universal Authentication Framework (UAF) protocol and the Universal Second Factor (U2F) protocol. While UAF focuses on passwordless authentication, U2F allows the addition of a second factor to existing password-based authentication. Both protocols are based on a public key cryptography challenge-response model.
UAF takes advantage of existing security technologies present on devices for authentication including fingerprint sensors, cameras(face biometrics), microphones(voice biometrics), Trusted Execution Environments(TEEs), Secure Elements(SEs) and others. The protocol is designed to plug-in these device capabilities into a common authentication framework. UAF works with both native applications and web applications. Download free codec player.
U2F augments password-based authentication using a hardware token (typically USB) that stores cryptographic authentication keys and uses them for signing. The user can use the same token as a second factor for multiple applications. U2F works with web applications. It provides protection against phishing by using the URL of the website to lookup the stored authentication key.
Session management is directly related to authentication. The Session Management General Guidelines previously available on this OWASP Authentication Cheat Sheet have been integrated into the Session Management Cheat Sheet.
Password managers are programs, browser plugins or web services that automate management of large number of different credentials, including memorizing and filling-in, generating random passwords on different sites etc. While use of password managers is subject to controversies and many organisations block their usage, their contribution to authentication security is positive, as pointed out by National Cyber Security Centre.
Web applications should at least not make password managers job more difficult than necessary by observing the following recommendations:
- use standard HTML forms for username and password input with appropriate
typeattributes, - do not artificially limit user passwords to a length 'reasonable for humans' and allow passwords lengths up to 128 characters,
- do not artificially prevent copy and paste on username and password fields,
- avoid plugin-based login pages (Flash, Silverlight etc)
As of 2017 Credential Management Level 1 standard for web browsers is being developed that may further facilitate interaction between password managers and complex log-in schemes (e.g. single sign-on).
Eoin Keary eoinkeary
Jim Manico
Timo Goosen
Pawel Krawczyk Free antivirus and malware removal software.
Sven Neuhaus
Manuel Aude Morales
This article provides a simple positive model for preventing XSS using output escaping/encoding properly. While there are a huge number of XSS attack vectors, following a few simple rules can completely defend against this serious attack.
This article does not explore the technical or business impact of XSS. Suffice it to say that it can lead to an attacker gaining the ability to do anything a victim can do through their browser.
Both reflected and stored XSS can be addressed by performing the appropriate validation and escaping on the server-side. DOM Based XSS can be addressed with a special subset of rules described in the DOM based XSS Prevention Cheat Sheet.
For a cheatsheet on the attack vectors related to XSS, please refer to the XSS Filter Evasion Cheat Sheet. More background on browser security and the various browsers can be found in the Browser Security Handbook.
Before reading this cheatsheet, it is important to have a fundamental understanding of Injection Theory.
A Positive XSS Prevention Model
This article treats an HTML page like a template, with slots where a developer is allowed to put untrusted data. These slots cover the vast majority of the common places where a developer might want to put untrusted data. Putting untrusted data in other places in the HTML is not allowed. This is a 'whitelist' model, that denies everything that is not specifically allowed.
Given the way browsers parse HTML, each of the different types of slots has slightly different security rules. When you put untrusted data into these slots, you need to take certain steps to make sure that the data does not break out of that slot into a context that allows code execution. In a way, this approach treats an HTML document like a parameterized database query - the data is kept in specific places and is isolated from code contexts with escaping.
This document sets out the most common types of slots and the rules for putting untrusted data into them safely. Based on the various specifications, known XSS vectors, and a great deal of manual testing with all the popular browsers, we have determined that the rules proposed here are safe.
The slots are defined and a few examples of each are provided. Developers SHOULD NOT put data into any other slots without a very careful analysis to ensure that what they are doing is safe. Browser parsing is extremely tricky and many innocuous looking characters can be significant in the right context.
Why Can't I Just HTML Entity Encode Untrusted Data?
HTML entity encoding is okay for untrusted data that you put in the body of the HTML document, such as inside a <div> tag. It even sort of works for untrusted data that goes into attributes, particularly if you're religious about using quotes around your attributes. But HTML entity encoding doesn't work if you're putting untrusted data inside a <script>tag anywhere, or an event handler attribute like onmouseover, or inside CSS, or in a URL. So even if you use an HTML entity encoding method everywhere, you are still most likely vulnerable to XSS. You MUST use the escape syntax for the part of the HTML document you're putting untrusted data into. That's what the rules below are all about.
You Need a Security Encoding Library
Writing these encoders is not tremendously difficult, but there are quite a few hidden pitfalls. For example, you might be tempted to use some of the escaping shortcuts like ' in JavaScript. However, these values are dangerous and may be misinterpreted by the nested parsers in the browser. You might also forget to escape the escape character, which attackers can use to neutralize your attempts to be safe. OWASP recommends using a security-focused encoding library to make sure these rules are properly implemented.
Microsoft provides an encoding library named the Microsoft Anti-Cross Site Scripting Library for the .NET platform and ASP.NET Framework has built-in ValidateRequest function that provides limited sanitization.
The OWASP Java Encoder Project provides a high-performance encoding library for Java.
The following rules are intended to prevent all XSS in your application. While these rules do not allow absolute freedom in putting untrusted data into an HTML document, they should cover the vast majority of common use cases. You do not have to allow all the rules in your organization. Many organizations may find that allowing only Rule #1 and Rule #2 are sufficient for their needs. Please add a note to the discussion page if there is an additional context that is often required and can be secured with escaping.
Do NOT simply escape the list of example characters provided in the various rules. It is NOT sufficient to escape only that list. Blacklist approaches are quite fragile. The whitelist rules here have been carefully designed to provide protection even against future vulnerabilities introduced by browser changes.
RULE #0 - Never Insert Untrusted Data Except in Allowed Locations
The first rule is to deny all - don't put untrusted data into your HTML document unless it is within one of the slots defined in Rule #1 through Rule #5. The reason for Rule #0 is that there are so many strange contexts within HTML that the list of escaping rules gets very complicated. We can't think of any good reason to put untrusted data in these contexts. This includes 'nested contexts' like a URL inside a javascript -- the encoding rules for those locations are tricky and dangerous.
If you insist on putting untrusted data into nested contexts, please do a lot of cross-browser testing and let us know what you find out.
Directly in a script:
Inside an HTML comment:
In an attribute name:
In a tag name:
Directly in CSS:
Most importantly, never accept actual JavaScript code from an untrusted source and then run it. For example, a parameter named 'callback' that contains a JavaScript code snippet. No amount of escaping can fix that.
RULE #1 - HTML Escape Before Inserting Untrusted Data into HTML Element Content
Rule #1 is for when you want to put untrusted data directly into the HTML body somewhere. This includes inside normal tags like div, p, b, td, etc. Most web frameworks have a method for HTML escaping for the characters detailed below. However, this is absolutely not sufficient for other HTML contexts. You need to implement the other rules detailed here as well.
Escape the following characters with HTML entity encoding to prevent switching into any execution context, such as script, style, or event handlers. Using hex entities is recommended in the spec. In addition to the 5 characters significant in XML (&, <, >, ', '), the forward slash is included as it helps to end an HTML entity.
RULE #2 - Attribute Escape Before Inserting Untrusted Data into HTML Common Attributes
Rule #2 is for putting untrusted data into typical attribute values like width, name, value, etc. This should not be used for complex attributes like href, src, style, or any of the event handlers like onmouseover. It is extremely important that event handler attributes should follow Rule #3 for HTML JavaScript Data Values.
Inside UNquoted attribute:
Inside single quoted attribute:
Inside double quoted attribute :
Except for alphanumeric characters, escape all characters with ASCII values less than 256 with the &#xHH; format (or a named entity if available) to prevent switching out of the attribute.
The reason this rule is so broad is that developers frequently leave attributes unquoted. Properly quoted attributes can only be escaped with the corresponding quote.
Unquoted attributes can be broken out of with many characters, including [space]%*+,-/;<=>^ and |.
RULE #3 - JavaScript Escape Before Inserting Untrusted Data into JavaScript Data Values
Rule #3 concerns dynamically generated JavaScript code - both script blocks and event-handler attributes. The only safe place to put untrusted data into this code is inside a quoted 'data value.' Including untrusted data inside any other JavaScript context is quite dangerous, as it is extremely easy to switch into an execution context with characters including (but not limited to) semi-colon, equals, space, plus, and many more, so use with caution.
Inside a quoted string:
One side of a quoted expression:
Inside quoted event handler:
Please note there are some JavaScript functions that can never safely use untrusted data as input - EVEN IF JAVASCRIPT ESCAPED!
For example:
Except for alphanumeric characters, escape all characters less than 256 with the xHH format to prevent switching out of the data value into the script context or into another attribute. DO NOT use any escaping shortcuts like ' because the quote character may be matched by the HTML attribute parser which runs first. These escaping shortcuts are also susceptible to escape-the-escape attacks where the attacker sends ' and the vulnerable code turns that into ' which enables the quote.
If an event handler is properly quoted, breaking out requires the corresponding quote. However, we have intentionally made this rule quite broad because event handler attributes are often left unquoted. Unquoted attributes can be broken out of with many characters including [space]%*+,-/;<=>^ and |.
Also, a </script> closing tag will close a script block even though it is inside a quoted string because the HTML parser runs before the JavaScript parser. Please note this is an aggressive escaping policy that over-encodes. If there is a guarantee that proper quoting is accomplished then a much smaller character set is needed. Please look at the OWASP Java Encoder JavaScript escaping examples for examples of proper JavaScript use that requires minimal escaping.
RULE #3.1 - HTML escape JSON values in an HTML context and read the data with JSON.parse
In a Web 2.0 world, the need for having data dynamically generated by an application in a javascript context is common. One strategy is to make an AJAX call to get the values, but this isn't always performant. Often, an initial block of JSON is loaded into the page to act as a single place to store multiple values. This data is tricky, though not impossible, to escape correctly without breaking the format and content of the values.
Ensure returned Content-Type header is application/json and not text/html. This shall instruct the browser not misunderstand the context and execute injected script
Bad HTTP response:
Good HTTP response:
A common anti-pattern one would see:
JSON serialization
A safe JSON serializer will allow developers to serialize JSON as string of literal JavaScript which can be embedded in an HTML in the contents of the <script> tag. HTML characters and JavaScript line terminators need be escaped. Consider the Yahoo JavaScript Serializer for this task.
HTML entity encoding
This technique has the advantage that html entity escaping is widely supported and helps separate data from server side code without crossing any context boundaries. Consider placing the JSON block on the page as a normal element and then parsing the innerHTML to get the contents. The javascript that reads the span can live in an external file, thus making the implementation of CSP enforcement easier.
An alternative to escaping and unescaping JSON directly in JavaScript, is to normalize JSON server-side by converting < to u003c before delivering it to the browser.
RULE #4 - CSS Escape And Strictly Validate Before Inserting Untrusted Data into HTML Style Property Values
Rule #4 is for when you want to put untrusted data into a stylesheet or a style tag. CSS is surprisingly powerful, and can be used for numerous attacks. Therefore, it's important that you only use untrusted data in a property value and not into other places in style data. You should stay away from putting untrusted data into complex properties like url, behavior, and custom (-moz-binding).
You should also not put untrusted data into IE’s expression property value which allows JavaScript.
Property value:
Please note there are some CSS contexts that can never safely use untrusted data as input - EVEN IF PROPERLY CSS ESCAPED! You will have to ensure that URLs only start with http not javascript and that properties never start with 'expression'.
For example:
Except for alphanumeric characters, escape all characters with ASCII values less than 256 with the HH escaping format. DO NOT use any escaping shortcuts like ' because the quote character may be matched by the HTML attribute parser which runs first. These escaping shortcuts are also susceptible to escape-the-escape attacks where the attacker sends ' and the vulnerable code turns that into ' which enables the quote.
If attribute is quoted, breaking out requires the corresponding quote. All attributes should be quoted but your encoding should be strong enough to prevent XSS when untrusted data is placed in unquoted contexts.
Unquoted attributes can be broken out of with many characters including [space]%*+,-/;<=>^ and |.
Also, the </style> tag will close the style block even though it is inside a quoted string because the HTML parser runs before the JavaScript parser. Please note that we recommend aggressive CSS encoding and validation to prevent XSS attacks for both quoted and unquoted attributes.
RULE #5 - URL Escape Before Inserting Untrusted Data into HTML URL Parameter Values
Rule #5 is for when you want to put untrusted data into HTTP GET parameter value.
Except for alphanumeric characters, escape all characters with ASCII values less than 256 with the %HH escaping format. Including untrusted data in data: URLs should not be allowed as there is no good way to disable attacks with escaping to prevent switching out of the URL.
All attributes should be quoted. Unquoted attributes can be broken out of with many characters including [space]%*+,-/;<=>^ and |. Note that entity encoding is useless in this context.
WARNING: Do not encode complete or relative URL's with URL encoding! If untrusted input is meant to be placed into href, src or other URL-based attributes, it should be validated to make sure it does not point to an unexpected protocol, especially javascript links. URL's should then be encoded based on the context of display like any other piece of data. For example, user driven URL's in HREF links should be attribute encoded.
For example:
RULE #6 - Sanitize HTML Markup with a Library Designed for the Job
If your application handles markup -- untrusted input that is supposed to contain HTML -- it can be very difficult to validate. Encoding is also difficult, since it would break all the tags that are supposed to be in the input. Therefore, you need a library that can parse and clean HTML formatted text. There are several available at OWASP that are simple to use:
An open-source .Net library. The HTML is cleaned with a white list approach. All allowed tags and attributes can be configured. The library is unit tested with the OWASP XSS Filter Evasion Cheat Sheet
For more information on OWASP Java HTML Sanitizer policy construction, see here.
The SanitizeHelper module provides a set of methods for scrubbing text of undesired HTML elements.
Other libraries that provide HTML Sanitization include:
- HTML sanitizer from Google Closure Library
- PHP HTML Purifier.
- JavaScript/Node.js Bleach.
- Python Bleach.
RULE #7 - Prevent DOM-based XSS
Owasp Csrf Prevention Cheat Sheet 2020
For details on what DOM-based XSS is, and defenses against this type of XSS flaw, please see the OWASP article on DOM based XSS Prevention Cheat Sheet.
Bonus Rule #1: Use HTTPOnly cookie flag
Preventing all XSS flaws in an application is hard, as you can see. To help mitigate the impact of an XSS flaw on your site, OWASP also recommends you set the HTTPOnly flag on your session cookie and any custom cookies you have that are not accessed by any Javascript you wrote. This cookie flag is typically on by default in .NET apps, but in other languages you have to set it manually. For more details on the HTTPOnly cookie flag, including what it does, and how to use it, see the OWASP article on HTTPOnly.
Bonus Rule #2: Implement Content Security Policy
There is another good complex solution to mitigate the impact of an XSS flaw called Content Security Policy. It's a browser side mechanism which allows you to create source whitelists for client side resources of your web application, e.g. JavaScript, CSS, images, etc. CSP via special HTTP header instructs the browser to only execute or render resources from those sources.
For example this CSP:
Will instruct web browser to load all resources only from the page's origin and JavaScript source code files additionaly from static.domain.tld. For more details on Content Security Policy, including what it does, and how to use it, see this article on Content Security Policy.
Bonus Rule #3: Use an Auto-Escaping Template System
Many web application frameworks provide automatic contextual escaping functionality such as AngularJS strict contextual escaping and Go Templates. Use these technologies when you can.
Bonus Rule #4: Use the X-XSS-Protection Response Header
Owasp Csrf Prevention
This HTTP response header enables the Cross-site scripting (XSS) filter built into some modern web browsers. This header is usually enabled by default anyway, so the role of this header is to re-enable the filter for this particular website if it was disabled by the user.
Bonus Rule #5: Properly use modern JS frameworks like Angular (2+) or ReactJS
Modern javascript frameworks have pretty good XSS protection built in. It is important how to use them properly to benefit from it.
When using ReactJS do not use dangerouslySetInnerHTML. If you really, really really have to use dangerouslySetInnerHTML remember that now all framework protections are turned off and you have to escape or sanitize all the data by yourself.
For Angular (2+) remember to build Angular templates with -prod parameter (ng build --prod) in order to avoid template injection.
And also remember to update your framework to the newest version, with all possible bug fixes, as soon as possible.
| Data Type | Context | Code Sample | Defense |
|---|---|---|---|
| String | HTML Body | <span>UNTRUSTED DATA </span> | HTML Entity Encoding (rule #1). |
| String | Safe HTML Attributes | <input type='text' name='fname' value='UNTRUSTED DATA '> | Aggressive HTML Entity Encoding (rule #2), Only place untrusted data into a whitelist of safe attributes (listed below), Strictly validate unsafe attributes such as background, id and name. |
| String | GET Parameter | <a href='/site/search?value=UNTRUSTED DATA '>clickme</a> | URL Encoding (rule #5). |
| String | Untrusted URL in a SRC or HREF attribute | <a href='UNTRUSTED URL '>clickme</a> <iframe src='UNTRUSTED URL ' /> | Canonicalize input, URL Validation, Safe URL verification, Whitelist http and https URL's only (Avoid the JavaScript Protocol to Open a new Window), Attribute encoder. |
| String | CSS Value | html <div>Selection</div> | Strict structural validation (rule #4), CSS Hex encoding, Good design of CSS Features. |
| String | Javascript Variable | <script>var currentValue='UNTRUSTED DATA ';</script> <script>someFunction('UNTRUSTED DATA ');</script> | Ensure JavaScript variables are quoted, JavaScript Hex Encoding, JavaScript Unicode Encoding, Avoid backslash encoding (' or ' or |
| HTML | HTML Body | <div>UNTRUSTED HTML</div> | HTML Validation (JSoup, AntiSamy, HTML Sanitizer..). |
| String | DOM XSS | <script>document.write('UNTRUSTED INPUT: ' + document.location.hash );<script/> | DOM based XSS Prevention Cheat Sheet |
Owasp Csrf Prevention Cheat Sheet Pdf
The following snippets of HTML demonstrate how to safely render untrusted data in a variety of different contexts.
Safe HTML Attributes include:align, alink, alt, bgcolor, border, cellpadding, cellspacing, class, color, cols, colspan, coords, dir, face, height, hspace, ismap, lang, marginheight, marginwidth, multiple, nohref, noresize, noshade, nowrap, ref, rel, rev, rows, rowspan, scrolling, shape, span, summary, tabindex, title, usemap, valign, value, vlink, vspace, width.
Owasp Csrf Prevention Cheat Sheet Download
The purpose of output encoding (as it relates to Cross Site Scripting) is to convert untrusted input into a safe form where the input is displayed as data to the user without executing as code in the browser. The following charts details a list of critical output encoding methods needed to stop Cross Site Scripting.
| Encoding Type | Encoding Mechanism |
|---|---|
| HTML Entity Encoding | Convert & to &, Convert < to <, Convert > to >, Convert ' to ", Convert ' to ', Convert / to / |
| HTML Attribute Encoding | Except for alphanumeric characters, escape all characters with the HTML Entity &#xHH; format, including spaces. (HH = Hex Value) |
| URL Encoding | Standard percent encoding, see here. URL encoding should only be used to encode parameter values, not the entire URL or path fragments of a URL. |
| JavaScript Encoding | Except for alphanumeric characters, escape all characters with the uXXXX unicode escaping format (X = Integer). |
| CSS Hex Encoding | CSS escaping supports XX and XXXXXX. Using a two character escape can cause problems if the next character continues the escape sequence. There are two solutions (a) Add a space after the CSS escape (will be ignored by the CSS parser) (b) use the full amount of CSS escaping possible by zero padding the value. |
XSS Attack Cheat Sheet
The following article describes how to exploit different kinds of XSS Vulnerabilities that this article was created to help you avoid:
- OWASP: XSS Filter Evasion Cheat Sheet - Based on - RSnake's: 'XSS Cheat Sheet'.
Description of XSS Vulnerabilities
- OWASP article on XSS Vulnerabilities.
Discussion on the Types of XSS Vulnerabilities
- Types of Cross-Site Scripting.
How to Review Code for Cross-site scripting Vulnerabilities
- OWASP Code Review Guide article on Reviewing Code for Cross-site scripting Vulnerabilities.
How to Test for Cross-site scripting Vulnerabilities
- OWASP Testing Guide article on Testing for Cross site scripting Vulnerabilities.
Jeff Williams - jeff.williams@contrastsecurity.com
Jim Manico - jim@owasp.org
Neil Mattatall - neil@owasp.org
